Microsoft Security Operations Analyst (SC-200)
The Microsoft Security Operations Analyst (SC-200) certification is designed for security professionals who specialize in monitoring and responding to security incidents using Microsoft security technologies.
The purpose of the certification is to validate the skills and knowledge required to implement, manage, and monitor security and compliance solutions in a Microsoft environment. The Microsoft Security Operations Analyst (SC-200) certification covers topics such as incident response, threat intelligence, cloud security, data governance, and compliance management.
The benefits of the SC-200 certification include demonstrating proficiency in Microsoft security technologies and improving career opportunities in the cybersecurity industry. The certification also provides access to Microsoft resources and communities, enabling professionals to stay up-to-date with the latest security trends and technologies. Additionally, earning the certification can enhance an organization’s security posture by ensuring that its security professionals have the necessary skills to effectively monitor and respond to security incidents.
Skills Acquired
Below is the list of skills and knowledge you will learn:
- Firstly, as a Microsoft Security Operations Analyst, you will be required to perform threat management, monitoring, and response by using a variety of security solutions across their environment.
- The role primarily investigates, responds to, and hunts for threats using Microsoft Azure Sentinel, Azure Defender, Microsoft 365 Defender, and third-party security products.
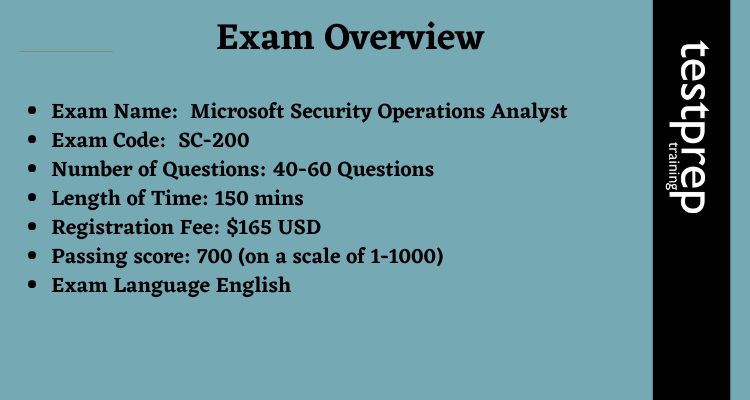
Exam Overview
- Firstly, the Microsoft Security Operations Analyst examination (SC-200) exam fee is $165 USD.
- Secondly, talking about the Microsoft Security Operations Analyst exam questions, there will be 40-60 questions.
- Thirdly, the exam is available in the English language only.
- Next, the passing mark for Microsoft Security Operations Analyst is 700 on a scale of 1-1000.
- Lastly, the SC-200 exam format is multiple choice and multiple response questions.
SC-200 Exam Glossary
Here’s a glossary of key terms related to the Microsoft Security Operations Analyst (SC-200) exam:
- Cloud Security – Refers to the protection of data, applications, and infrastructure in cloud computing environments.
- Compliance – Refers to the adherence to industry standards, laws, and regulations related to data security and privacy.
- Cybersecurity – Refers to the protection of computer systems, networks, and data from unauthorized access, theft, and damage.
- Data Governance – Refers to the process of managing the availability, usability, integrity, and security of data used in an organization.
- Identity and Access Management (IAM) – Refers to the process of managing user identities and access to resources within an organization.
- Incident Response – Refers to the process of responding to and managing security incidents, such as data breaches or malware infections.
- Network Security – Refers to the protection of computer networks from unauthorized access, theft, and damage.
- Penetration Testing – Refers to the process of testing the security of computer systems and networks by attempting to exploit vulnerabilities.
- Risk Management – Refers to the process of identifying, assessing, and mitigating risks to an organization’s assets, including data, systems, and infrastructure.
- Threat Intelligence – Refers to the process of collecting, analyzing, and sharing information about potential security threats and vulnerabilities.
Exam Registration
For registering yourself for Microsoft Security Operations Analyst (SC-200) you are required to follow the following steps:
- You can book your examination with Pearson VUE.
- Click on Schedule your exam on the official Microsoft page.
- Login in your Microsoft account using your email id, if you haven’t created an account on Microsoft you are required to signup first before login in. Also, select the examination by entering the exam code SC-200 or the examination name, i.e., Microsoft Security Operations Analyst.
- Follow the instructions given on the site and select the available date and time slot and make the payment.
Exam Policies
The candidate is recommended to read these policies so as to avoid any kind of confusion in the future.These policies contain information about registration options, learning credits, etc.
Exam Retake Policy
If the candidate failed to achieve the passing score, then he/she has to wait for 24 hours before reapplying to the examination. The candidate can go to their certificate dashboard and reschedule the exam themselves. The candidate can reappear for the examination only five times. Failure in the second attempt will result in a waiting time of 14 days before rescheduling your third attempt. The waiting period for the fourth and the fifth attempts will also be 14 days.
Exam Cancellation Policy
Microsoft offers candidates to cancel or reschedule their exams within a minimum of 24 hours prior to the exam date. However, to prevent any cancellation fee, you must cancel or reschedule your exam, at least 6 business days prior to the date scheduled for your exam. Also, if you fail to appear in the exam, then you will not receive any refund of the exam fee.
Recertification Policy
Microsoft certification is expected to expire when the products are out of mainstream support although the person`s certification will be recognized. Officially, the certification will never expire.
To check the full Microsoft Policies, click here.
For more information, click on Microsoft Security Operations Analyst (SC-200) FAQ.
Course Outline for Microsoft Security Operations Analyst Exam (SC-200)
The SC-200 covers the following topics:
Mitigate threats by using Microsoft 365 Defender (25-30%)
Mitigate threats to the Microsoft 365 environment by using Microsoft 365 Defender
- Investigate, respond, and remediate threats to Microsoft Teams, SharePoint, and OneDrive (Microsoft Documentation: Threat investigation and response)
- Investigate, respond, and remediate threats to email by using Microsoft Defender for Office 365 (Microsoft Documentation: Automated investigation and response (AIR) in Microsoft Defender for Office 365)
- Investigate and respond to alerts generated from Data Loss Prevention (DLP) policies (Microsoft Documentation: Configure and view alerts for data loss prevention polices)
- Investigate and respond to alerts generated from insider risk policies (Microsoft Documentation: Get started with insider risk management)
- Discover and manage apps by using Microsoft Defender for Cloud Apps
- Identify, investigate, and remediate security risks by using Defender for Cloud Apps (Microsoft Documentation: Investigate)
Mitigate endpoint threats by using Microsoft Defender for Endpoint
- Manage data retention, alert notification, and advanced features (Microsoft Documentation: Understanding what is Microsoft’s data retention policy?, Understanding Update data retention settings for Endpoint, Understanding Configure alert notifications, Understanding Manage Microsoft Defender for Endpoint alerts, Understanding Configure advanced features in Defender for Endpoint)
- Recommend attack surface reduction (ASR) for devices
- Respond to incidents and alerts (Microsoft Documentation: Incident response with Microsoft 365 Defender)
- Configure and manage device groups
- Identify devices at risk by using the Microsoft Defender Vulnerability Management
- Manage endpoint threat indicators (Microsoft Documentation: Create indicators, Manage indicators)
- Identify unmanaged devices by using device discovery
Manage identity threats
- Mitigate security risks related to events for Microsoft Entra ID
- Mitigate security risks related to Microsoft Entra Identity Protection events
- Mitigate security risks related to Active Directory Domain Services (AD DS) by using Microsoft Defender for Identity
Manage extended detection and response (XDR) in Microsoft 365 Defender
- Manage incidents and automated investigations in the Microsoft 365 Defender portal
- Manage actions and submissions in the Microsoft 365 Defender portal
- Identify threats by using Kusto Query Language (KQL)
- Identify and remediate security risks using Microsoft Secure Score (Microsoft Documentation: Security posture for Microsoft Defender for Cloud, Microsoft Secure Score)
- Analyze threat analytics in the Microsoft 365 Defender portal (Microsoft Documentation: Threat analytics in Microsoft 365 Defender)
- Configure and manage custom detections and alerts (Microsoft Documentation: Create and manage custom detections rules)
Investigate threats by using audit features in Microsoft 365 Defender and Microsoft Purview
- Perform threat hunting by using UnifiedAuditLog
- Perform threat hunting by using Content Search
Mitigate threats by using Microsoft Defender for Cloud (15-20%)
Implement and maintain cloud security posture management
- Assign and manage regulatory compliance policies, including Microsoft cloud security benchmark (MCSB)
- Improve the Microsoft Defender for Cloud secure score by applying recommended remediations
- Configure and manage Microsoft Defender for DevOps
- Configure and manage Microsoft Defender External Attack Surface Management (EASM)
Configure environment settings in Defender for Cloud
- Plan and configure Defender for Cloud settings, including selecting target subscriptions and workspaces (Microsoft Documentation: Enable enhanced security features)
- Configure Microsoft Defender for Cloud roles (Microsoft Documentation: Permissions in Microsoft Defender for Cloud, Enable enhanced security features)
- Assess and recommend cloud workload protection (Microsoft Documentation: Microsoft Defender for Cloud)
- Enable Microsoft Defender plans for Defender for Cloud
- Configure automated onboarding for Azure resources
- Connect compute resources by using Azure Arc
- Connect multicloud resources by using Environment settings
Respond to alerts and incidents in Defender for Cloud
- Setup email notifications (Microsoft Documentation: Understanding Configure email notifications for security alerts)
- Create and manage alert suppression rules (Microsoft Documentation: Understanding Suppress alerts from Azure Defender, Understanding Manage suppression rules)
- Design and configure workflow automation in Defender for Cloud (Microsoft Documentation: Automate responses to Microsoft Defender for Cloud triggers)
- Remediate alerts and incidents by using Defender for Cloud recommendations (Microsoft Documentation: Security alerts and incidents)
- Manage security alerts and incidents (Microsoft Documentation: Manage and respond to security alerts in Microsoft Defender for Cloud)
- Analyze Defender for Cloud threat intelligence reports (Microsoft Documentation: Microsoft Defender for Cloud threat intelligence report)
Mitigate threats by using Microsoft Sentinel (50-55%)
Design and configure a Microsoft Sentinel workspace
- Firstly, plan a Microsoft Sentinel workspace (Microsoft Documentation: Create and manage Microsoft Sentinel workspaces)
- Secondly, configure Microsoft Sentinel roles (Microsoft Documentation: Roles and permissions in Microsoft Sentinel)
- Design and configure Azure Sentinel data storage, including log types and log retention
Plan and Implement the use of Data Connectors for Ingestion of Data Sources in Microsoft Sentinel
- identify data sources to be ingested for Microsoft Sentinel (Microsoft Documentation: Understanding Connect data sources)
- configure and use Microsoft Sentinel data connectors for Azure resources, including Azure Policy and diagnostic settings
- Configure Microsoft Sentinel connectors for Microsoft 365 Defender and Defender for Cloud (Microsoft Documentation: Connect data from Microsoft 365 Defender to Microsoft Sentinel)
- Design and configure Syslog and Common Event Format (CEF) event collections (Microsoft Documentation: Understanding Collect data from Linux-based sources using Syslog, Understanding Connect your external solution using Common Event Format, Understanding Best Practices for CEF collection in Azure Sentinel)
- Design and Configure Windows Events collections (Microsoft Documentation: Understanding Connect Windows security events)
- Configure threat intelligence connectors
- Create custom log tables in the workspace to store ingested data
Manage Microsoft Sentinel analytics rules
- Configure the Fusion rule
- Configure Microsoft security analytics rules
- Configure built-in scheduled queries rules
- Configure custom scheduled queries rules (Microsoft Documentation: Understanding Create a custom analytics rule with a scheduled query)
- Configure near-real-time (NRT) query rules
- Manage analytics rules from Content hub
- Manage and use watchlists (Microsoft Documentation: Use watchlists in Microsoft Sentinel)
- Manage and use threat indicators (Microsoft Documentation: Create indicators, Manage indicators)
Perform data classification and normalization
- Classify and analyze data by using entities (Microsoft Documentation: Classify and analyze data using entities in Microsoft Sentinel)
- Query Microsoft Sentinel data by using Advanced Security Information Model (ASIM) parsers (Microsoft Documentation: Using the Advanced Security Information Model (ASIM) (Public preview))
- Develop and manage ASIM parsers (Microsoft Documentation: Using the Advanced Security Information Model (ASIM))
Configure Security Orchestration Automated Response (SOAR) in Microsoft Sentinel
- Create and configure automation rules (Microsoft Documentation: Create and use Microsoft Sentinel automation rules to manage response)
- Create and configure Microsoft Sentinel playbooks (Microsoft Documentation: Automate threat response with playbooks in Microsoft Sentinel, Create and use Microsoft Sentinel automation rules to manage response)
- Configure analytic rules to trigger automation rules
- Trigger playbooks manually from alerts and incidents
Manage Microsoft Sentinel Incidents
- Create an incident
- Triage incidents in Microsoft Sentinel (Microsoft Documentation: Understanding Triage security alerts)
- Investigate incidents in Microsoft Sentinel (Microsoft Documentation: Investigate incidents with Microsoft Sentinel)
- respond to incidents in Microsoft Sentinel (Microsoft Documentation: Investigate incidents with Microsoft Sentinel)
- investigate multi-workspace incidents (Microsoft Documentation: Understanding Work with incidents in many workspaces at once)
Use Microsoft Sentinel workbooks to analyze and interpret data
- Firstly, activate and customize Microsoft Sentinel workbook templates (Microsoft Documentation: Use Azure Monitor workbooks to visualize and monitor your data)
- Secondly, create custom workbooks (Microsoft Documentation: Understanding Create new workbooks)
- Next, configure advanced visualizations (Microsoft Documentation: Understanding Query and visualize data with Azure Sentinel Workbooks)
Hunt for threats using the Microsoft Sentinel
- Analyze attack vector coverage by using MITRE ATT&CK in Microsoft Sentinel
- Customize content gallery hunting queries
- Create custom hunting queries (Microsoft Documentation: Understanding Create custom queries to refine threat hunting)
- use hunting bookmarks for data investigations (Microsoft Documentation: Understanding Explore bookmarks in the investigation graph)
- Monitor hunting queries by using Livestream (Microsoft Documentation: Understanding Manage hunting and Livestream queries in Azure Sentinel)
- Retrieve and manage archived log data
- Create and manage search jobs
Manage threats by using entity behavior analytics
- Configure entity behavior settings
- Investigate threats by using entity pages
- Configure anomaly detection analytics rules
Preparatory Guide for Microsoft Security Operations Analyst (SC-200)
To pass any exam, you must have a well-thought-out strategy and study guide. There is an unending array of resources available to help you prepare for the exam. You must prepare, practice, and work hard in order to pass the Microsoft Security Operations Analyst Exam (SC-200). This guide will assist you during your preparation for this exam and serve as a springboard for future professional opportunities. Let’s take it one step at a time:
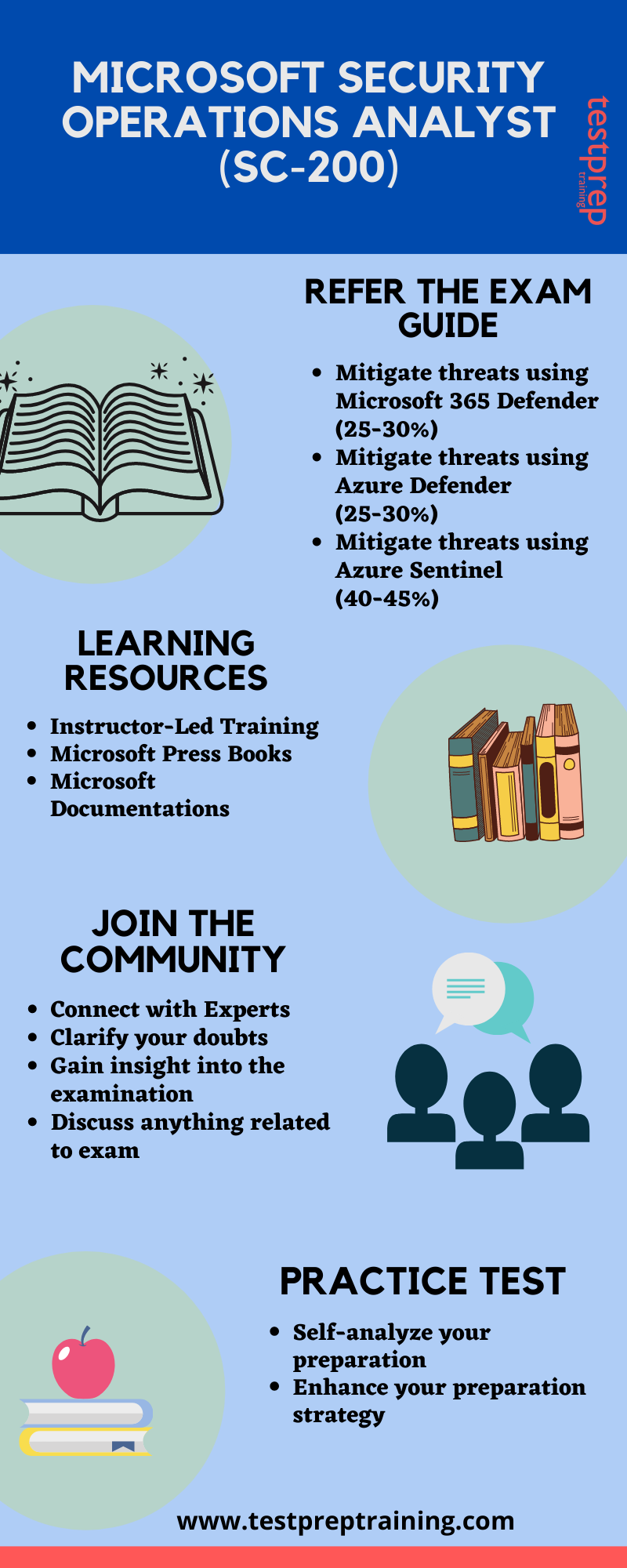
Instructor-led Training
Microsoft offers instructor-led training for the SC-200 examination. It is a four-day training The instructor-led training is an important resource in order to grt a better and deep understanding of the examination. After completion of this training you willbe able to:
- Explain how Microsoft Defender for Endpoint can remediate risks in your environment
- Create a Microsoft Defender for the Endpoint environment
- Configure Attack Surface Reduction rules on Windows 10 devices
Microsoft Books
Microsoft offers reference materials that might be helpful for test preparation. Numerous valuable materials that may be applied in the classroom are provided by these books. You may find pertinent publications that will aid in your comprehension of the test’s goals, help you pass the exam, and help you get your certification by visiting Microsoft Press publications. There are other books for the Microsoft SC-200 available on Amazon.com. You may use these books as a Microsoft SC-200 study guide to help you get ready for the test in a methodical way.
Familiarize yourself with Microsoft security technologies
Become familiar with the Microsoft security technologies covered on the exam, such as Azure Sentinel, Microsoft Defender for Endpoint, and Microsoft 365 Defender. Obtain practical experience by working on security-related projects, performing security assessments, or participating in security-related events.
Join Microsoft Community
A robust debate is always useful, regardless of where it takes place. When a large number of people get involved in a problem, the chances of finding a solution grow dramatically. The research gets more extensive as a result of these conversations. Forums are excellent for forming a community that is necessary for understanding others. Interacting with others who have the same goals as you take you one step closer to accomplishing them. You should consider joining the Microsoft Community.
Practice Test Papers
The final stage to success is to put what you’ve learned into practice. Using a Microsoft SC-200 practice exam to diversify your study method and achieve the best possible outcomes on the real thing is a terrific approach to achieve the best possible results. Furthermore, in order to ensure comprehensive preparation, it is critical to analyze the practice test. We offer free Microsoft SC-200 practice tests to assist you in passing the exam.
SC-200 Exam Final Tips
Here are some final tips and advice for success on the Microsoft Security Operations Analyst (SC-200) certification exam:
- Read the exam questions carefully: Take the time to carefully read each exam question and understand what is being asked.
- Manage your time wisely: Manage your time wisely during the exam to ensure that you have enough time to complete all the questions.
- Focus on the exam objectives: Focus on the exam objectives and ensure that you have a good understanding of the knowledge and skills that will be tested.
- Practice with sample questions: Practice with sample questions to get a sense of the type of questions that will be asked on the exam.
- Utilize exam study resources: Utilize exam study resources such as Microsoft documentation, training courses, and practice exams to enhance your understanding of the exam content.
- Take breaks: Take breaks during the exam to rest and refocus your mind.
- Don’t leave any questions unanswered: Make sure to answer all questions, even if you are not sure of the correct answer.
- Stay calm and focused: Stay calm and focused during the exam to avoid becoming overwhelmed or distracted.
By following these tips and putting in the necessary time and effort to prepare for the exam, you can increase your chances of success and demonstrate your expertise in Microsoft security technologies and security operations analysis.