Microsoft Azure is one of the most popular cloud computing platforms in the world. With the increasing demand for cloud-based solutions, the demand for professionals with Azure certifications has also been on the rise. The Microsoft Azure AZ-500 exam is one such certification that validates the skills of professionals in securing the Azure environment.
The exam tests a candidate’s knowledge and skills in implementing security controls, securing data and applications, managing identities, and protecting networks and systems on the Azure platform. It is designed for security engineers, security administrators, and other professionals responsible for managing Azure security.
But how hard is the Microsoft Azure AZ-500 exam? In this blog, we will explore the exam format, the topics covered, and the difficulty level of the exam, to help you better understand what to expect when preparing for this certification.
Microsoft Azure AZ-500 Exam Overview
The Microsoft Azure AZ-500 exam is for professionals who want to demonstrate their knowledge in deploying, installing, administering, and managing Microsoft Azure software. It certifies candidates in security controls implementation, security posture maintenance, identity and access management, data protection, applications, and networks. The exam is based on a Microsoft Security Engineer’s job description. This test assesses your ability to perform technical activities in the employment function.
Microsoft Azure (AZ-500) Glossary
Here is a glossary of terms related to Microsoft Azure (AZ-500):
- Azure: Microsoft’s cloud computing platform that provides a wide range of services and features for building, deploying, and managing applications and services.
- Azure AD: Azure Active Directory is a cloud-based identity and access management (IAM) service that helps organizations to manage users and access to resources.
- Azure Policy: A service that helps organizations to enforce and maintain compliance with corporate policies and industry standards across their Azure resources.
- Azure Resource Manager (ARM): A service that provides a unified management layer for organizing and deploying Azure resources.
- Azure Security Center: A unified security management system that provides advanced threat protection and security management across hybrid cloud workloads.
- Azure Virtual Machines: Azure VMs are on-demand, scalable computing resources that enable organizations to run workloads in the cloud.
- Azure Backup: A cloud-based backup service that provides reliable, scalable, and cost-effective backup and restore solutions for your data and applications.
- Azure Load Balancer: A service that distributes incoming traffic across multiple resources, such as virtual machines, to improve availability and performance.
- Azure Site Recovery: A disaster recovery solution that provides automated replication and failover of virtual machines and physical servers to Azure.
- Azure ExpressRoute: A service that provides a dedicated, private connection between on-premises infrastructure and Azure datacenters, which can improve network performance, reliability, and security.
- Azure Key Vault: A cloud-based service that enables organizations to securely store and manage cryptographic keys, certificates, and secrets.
- Azure DDoS Protection: A service that provides protection against distributed denial of service (DDoS) attacks, which can disrupt availability of your services.
- Azure Firewall: A cloud-based network security service that provides centralized network security management and protection for your Azure resources.
- Azure Storage: A cloud-based storage service that provides scalable, secure, and highly available storage for your data.
- Azure SQL Database: A cloud-based relational database service that provides scalable, secure, and highly available database solutions for your applications.
- Azure DevOps: A cloud-based collaboration and software development platform that provides tools for planning, building, and deploying software applications.
- Azure Kubernetes Service (AKS): A fully managed Kubernetes container orchestration service that enables organizations to deploy and manage containerized applications in Azure.
- Azure Functions: A serverless computing service that enables organizations to run event-driven code without provisioning or managing infrastructure.
- Azure Cosmos DB: A globally distributed, multi-model database service that provides scalable, highly available, and low-latency database solutions for your applications.
- Azure Cognitive Services: A collection of cloud-based APIs and services that enable organizations to build intelligent applications using natural language processing, computer vision, and other AI technologies.
Exam preparation resources for Microsoft Azure AZ-500 Exam
Here are some exam preparation resources for the Microsoft Azure AZ-500 certification exam:
- Official Microsoft Exam Page: The official page for the AZ-500 exam, which includes information about the exam structure, skills measured, and registration information. Link: https://docs.microsoft.com/en-us/learn/certifications/exams/az-500
- Microsoft Learning Path: The Microsoft Learning Path for the AZ-500 exam includes modules covering topics such as security management, identity and access management, platform protection, and data and application protection. Link: https://docs.microsoft.com/en-us/learn/certifications/azure-security-engineer
- Microsoft Azure Documentation: The Microsoft Azure Documentation provides in-depth information on all aspects of the Azure platform, including security features and best practices. Link: https://docs.microsoft.com/en-us/azure/?product=featured
- Microsoft Azure Blog: The Microsoft Azure Blog provides updates on new Azure features and services, including those related to security and compliance. Link: https://azure.microsoft.com/en-us/blog/
- Exam Ref Book: The “Exam Ref AZ-500 Microsoft Azure Security Technologies” book is a study guide written by Yuri Diogenes and Dr. Thomas W. Shinder. It provides comprehensive coverage of the exam objectives and includes practice questions. Link: https://www.microsoftpressstore.com/store/exam-ref-az-500-microsoft-azure-security-technologies-9780135764803
How hard is the Microsoft Azure AZ-500 Exam?
The Microsoft Azure AZ-500 exam is considered to be a challenging certification exam that tests a candidate’s knowledge and skills in implementing security controls, maintaining security posture, and managing identity and access in Microsoft Azure. The exam covers a wide range of topics, including Azure Active Directory, Azure Security Center, Azure Sentinel, Azure Virtual Networks, and more.
The difficulty level of the exam may vary depending on your level of experience and expertise with Microsoft Azure. For those who have hands-on experience with Azure security and related technologies, the exam may be less challenging, but for those who are new to Azure security, the exam may be more difficult.
However, with adequate preparation and study, including using Microsoft’s official exam study resources, practice exams, and hands-on experience with Azure security, you can increase your chances of passing the AZ-500 exam.
Microsoft Azure AZ-500 Exam Outline
Microsoft Azure Security Technologies (AZ-500) Exam covers the following topics –
Manage identity and access (25–30%)
Manage identities in Microsoft Entra ID
- Secure users in Microsoft Entra ID
- Secure directory groups in Microsoft Entra ID
- Recommend when to use external identities (Microsoft Documentation: External Identities in Azure Active Directory)
- Secure external identities
- Implement Microsoft Entra Identity Protection (Microsoft Documentation: What is Identity Protection)
Manage authentication by using Microsoft Entra ID
- Configure Microsoft Entra Verified ID (Microsoft Documentation: Configure your tenant for Microsoft Entra Verified ID)
- Implementing multi-factor authentication (MFA) (Microsoft Documentation: Azure AD Multi-Factor Authentication)
- Implement passwordless authentication (Microsoft Documentation: Enable passwordless sign-in with Microsoft Authenticator)
- Implement password protection (Microsoft Documentation: Enforce on-premises Azure AD Password Protection for Active Directory Domain Services)
- Implementing single sign-on (SSO) (Microsoft Documentation: What is single sign-on in Azure Active Directory?)
- Integrate single sign on (SSO) and identity providers
- Recommend and enforce modern authentication protocols (Microsoft Documentation: Block legacy authentication with Azure AD with Conditional Access)
Manage authorization by using Microsoft Entra ID
- Configure Azure role permissions for management groups, subscriptions, resource groups, and resources (Microsoft Documentation: What are Azure management groups)
- Assign built-in roles in Microsoft Entra ID
- Assign built-in roles in Azure
- Create and assign custom roles, including Azure roles and Microsoft Entra roles
- Implement and manage Microsoft Entra Permissions Management (Microsoft Documentation: What’s Permissions Management?)
- Configure Microsoft Entra Privileged Identity Management (PIM)
- Configure role management and access reviews by using Microsoft Entra (Microsoft Documentation: What are access reviews?)
- Implement Conditional Access policies (Microsoft Documentation: What is Conditional Access?)
Manage application access in Microsoft Entra ID
- Manage access to enterprise applications in Microsoft Entra ID, including OAuth permission grants (Microsoft Documentation: Grant tenant-wide admin consent to an application)
- Manage app registrations in Microsoft Entra ID
- Configure app registration permission scopes (Microsoft Documentation: Introduction to permissions and consent)
- Managing app registration permission consent (Microsoft Documentation: Configure how users consent to applications)
- Manage and use service principals (Microsoft Documentation: Application and service principal objects in Azure Active Directory)
- Manage managed identities for Azure resources (Microsoft Documentation: What are managed identities for Azure resources?)
- Recommend when to use and configure an Microsoft Entra Application Proxy, including authentication
Secure networking (20–25%)
Plan and Implement security for virtual networks
- Plan and implement Network Security Groups (NSGs) and Application Security Groups (ASGs) (Microsoft Documentation: Application security groups, Network security groups)
- Plan and implement user-defined routes (UDRs)
- Planning and implement VNET peering or VPN gateway (Microsoft Documentation: Configure a VNet-to-VNet VPN gateway connection by using the Azure portal)
- Plan and implement Virtual WAN, including a secured virtual hub (Microsoft Documentation: What is a secured virtual hub?)
- Secure VPN connectivity, including point-to-site and site-to-site (Microsoft Documentation: About Point-to-Site VPN, Create a site-to-site VPN connection)
- Implement encryption over ExpressRoute (Microsoft Documentation: ExpressRoute encryption)
- Configure firewall settings on PaaS resources (Microsoft Documentation: Configure Azure Storage firewalls and virtual networks)
- Monitor network security by using Network Watcher, including NSG flow logging (Microsoft Documentation: Introduction to flow logs for network security groups, Log network traffic to and from a virtual machine using the Azure portal)
Plan and implement security for private access to Azure resources
- Plan and implement virtual network Service Endpoints (Microsoft Documentation: Virtual Network service endpoints)
- Planning and implement Private Endpoints (Microsoft Documentation: What is a private endpoint?)
- Plan and implement Private Link services (Microsoft Documentation: What is Azure Private Link?)
- Plan and implement network integration for Azure App Service and Azure Functions
- Plan and implement network security configurations for an App Service Environment (ASE) (Microsoft Documentation: Networking considerations for App Service Environment, App Service Environment networking)
- Planning and implement network security configurations for an Azure SQL Managed Instance (Microsoft Documentation: Azure SQL Database and SQL Managed Instance security capabilities, Azure SQL Database security features)
Plan and implement security for public access to Azure resources
- Plan and implement Transport Layer Security (TLS) to applications, including Azure App Service and API Management (Microsoft Documentation: Add and manage TLS/SSL certificates in Azure App Service)
- Plan and implement, and manager an Azure Firewall including Azure Firewall Manager and firewall policies (Microsoft Documentation: What is Azure Firewall Manager?)
- Plan and implement an Azure Application Gateway (Microsoft Documentation: Application Gateway infrastructure configuration)
- Plan and implement an Azure Front Door, including Content Delivery Network (CDN)
- Plan and implement a Web Application Firewall (WAF) (Microsoft Documentation: What is Azure Web Application Firewall?)
- Recommend when to use Azure DDoS Protection Standard (Microsoft Documentation: Azure DDoS Protection)
Secure compute, storage, and databases (20–25%)
Plan and implement advanced security for compute
- Plan and implement remote access to public endpoints, including Azure Bastion and just-in-time (JIT) virtual machine (VM) access (Microsoft Documentation: What is Azure Bastion?, Plan for virtual machine remote access)
- Configure network isolation for Azure Kubernetes Service (AKS) (Microsoft Documentation: Network concepts for applications in Azure Kubernetes Service (AKS))
- Secure and monitor AKS (Microsoft Documentation: Monitoring Azure Kubernetes Service (AKS) with Azure Monitor)
- Configuring authentication for AKS (Microsoft Documentation: Access and identity options for Azure Kubernetes Service (AKS))
- Configure security monitoring for Azure Container Instances (ACIs)
- Configure security monitoring for Azure Container Apps (ACAs)
- Manage access to Azure Container Registry (ACR) (Microsoft Documentation: Azure Container Registry roles and permissions)
- Configure disk encryption, including Azure Disk Encryption (ADE), encryption as host, and confidential disk encryption (Microsoft Documentation: Overview of managed disk encryption options, Azure Disk Encryption for Windows VMs)
- Recommend security configurations for Azure API Management (Microsoft Documentation: Azure security baseline for API Management)
Plan and implement security for storage
- Configure access control for storage accounts (Microsoft Documentation: Authorize access to data in Azure Storage)
- Manage life cycle for storage account access keys (Microsoft Documentation: Optimize costs by automatically managing the data lifecycle)
- Selecting and configure an appropriate method for access to Azure Files (Microsoft Documentation: Mount SMB Azure file share on Windows)
- Select and configure an appropriate method for access to Azure Blob Storage (Microsoft Documentation: Authorize access to blobs using Azure Active Directory, Choose how to authorize access to blob data in the Azure portal)
- Select and configure an appropriate method for access to Azure Tables (Microsoft Documentation: Authorize access to tables using Azure Active Directory)
- Selecting and configure an appropriate method for access to Azure Queues (Microsoft Documentation: Get started with Azure Queue Storage using .NET)
- Select and configure appropriate methods for protecting against data security threats, including soft delete, backups, versioning, and immutable storage (Microsoft Documentation: Store business-critical blob data with immutable storage, Data protection overview)
- Configure Bring your own key (BYOK) (Microsoft Documentation: Bring your own key (BYOK) details for Azure Information Protection)
- Enable double encryption at the Azure Storage infrastructure level (Microsoft Documentation: Enable infrastructure encryption for double encryption of data)
Plan and implement security for Azure SQL Database and Azure SQL Managed Instance
- Enable database authentication by using Microsoft Entra ID
- Enable database auditing (Microsoft Documentation: Auditing for Azure SQL Database and Azure Synapse Analytics)
- Identify use cases for the Microsoft Purview governance portal (Microsoft Documentation: What’s available in the Microsoft Purview governance portal?)
- Implement data classification of sensitive information by using the Microsoft Purview governance portal (Microsoft Documentation: Data classification in the Microsoft Purview governance portal)
- Plan and implement dynamic masking (Microsoft Documentation: Dynamic Data Masking)
- Implement Transparent Database Encryption (TDE) (Microsoft Documentation: Transparent data encryption (TDE))
- Recommend when to use Azure SQL Database Always Encrypted (Microsoft Documentation: Always Encrypted)
Manage security operations (25–30%)
Plan, implement, and manage governance for security
- Create, assign, and interpret security policies and initiatives in Azure Policy (Microsoft Documentation: What is Azure Policy?)
- Configure security settings by using Azure Blueprint (Microsoft Documentation: What is Azure Blueprints?)
- Deploy secure infrastructures by using a landing zone (Microsoft Documentation: What is an Azure landing zone?)
- Create and configure an Azure Key Vault (Microsoft Documentation: About Azure Key Vault)
- Recommend when to use a dedicated Hardware Security Module (HSM) (Microsoft Documentation: What is Azure Dedicated HSM?)
- Configure access to Key Vault, including vault access policies and Azure Role-Based Access Control (Microsoft Documentation: Provide access to Key Vault keys, certificates, and secrets)
- Manage certificates, secrets, and keys (Microsoft Documentation: Azure Key Vault keys, secrets and certificates overview)
- Configure key rotation (Microsoft Documentation: Configure cryptographic key auto-rotation in Azure Key Vault)
- Configure backup and recovery of certificates, secrets, and keys
Manage security posture by using Microsoft Defender for Cloud
- Identify and remediate security risks by using the Microsoft Defender for Cloud Secure Score and Inventory (Microsoft Documentation: Security posture for Microsoft Defender for Cloud)
- Assess compliance against security frameworks and Microsoft Defender for Cloud (Microsoft Documentation: Improve your regulatory compliance)
- Add industry and regulatory standards to Microsoft Defender for Cloud
- Add custom initiatives to Microsoft Defender for Cloud (Microsoft Documentation: Create custom Azure security initiatives and policies)
- Connect hybrid cloud and multi-cloud environments to Microsoft Defender for Cloud (Microsoft Documentation: What is Microsoft Defender for Cloud?)
- Identify and monitor external assets by using Microsoft Defender External Attack Surface Management
Configure and manage threat protection by using Microsoft Defender for Cloud
- Enable workload protection services in Microsoft Defender for Cloud, including Microsoft Defender for Storage, Databases, Containers, App Service, Key Vault, Resource Manager, and DNS
- Configure Microsoft Defender for Servers (Microsoft Documentation: Onboard Windows servers to the Microsoft Defender for Endpoint service)
- Configure Microsoft Defender for Azure SQL Database (Microsoft Documentation: Microsoft Defender for SQL)
- Manage and respond to security alerts in Microsoft Defender for Cloud (Microsoft Documentation: Manage and respond to security alerts in Microsoft Defender for Cloud)
- Configure workflow automation by using Microsoft Defender for Cloud
- Evaluate vulnerability scans from Microsoft Defender for Server (Microsoft Documentation: Defender for Cloud’s integrated Qualys vulnerability scanner for Azure and hybrid machines)
Configure and manage security monitoring and automation solutions
- Monitor security events by using Azure Monitor (Microsoft Documentation: Azure Monitor overview)
- Configure data connectors in Microsoft Sentinel (Microsoft Documentation: Microsoft Sentinel data connectors)
- Create and customize analytics rules in Microsoft Sentinel (Microsoft Documentation: Create custom analytics rules to detect threats)
- Evaluate alerts and incidents in Microsoft Sentinel (Microsoft Documentation: Investigate incidents with Microsoft Sentinel)
- Configure automation in Microsoft Sentinel
How difficult is the Microsoft Azure AZ-500 exam?
Now that we have covered all the aspects of the exam, we can come to the main question – How difficult is the Microsoft Azure AZ-500 exam? The answer to this is, that it is quite a tough exam to crack. You will be thoroughly tested for your knowledge and technical skills. And it will take quite an effort to cover all the domains of the course outline.
However, when we say it’s tough, it doesn’t mean it is an unachievable feat. With dedication and determination, you can emerge out successful. Just that you have to keep your efforts targeted towards the goals and get your hands on ideal preparation resources.
Microsoft Azure AZ-500 Study Guide
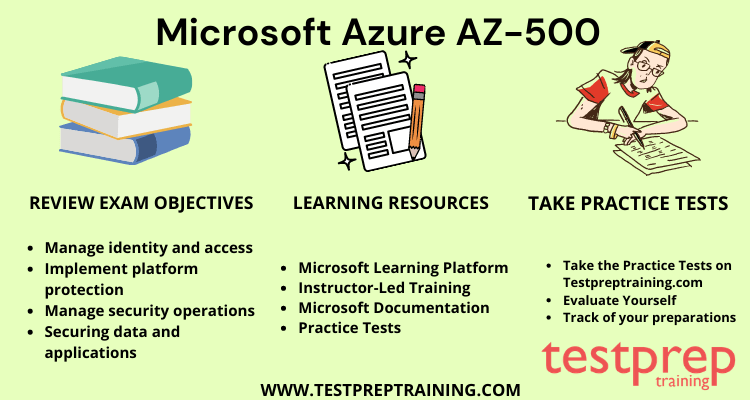
The learning resources will have the biggest impact on the quality of your preparations. Consequently, it is essential to use reliable resources. With devoted efforts and the right learning content, you can prepare yourself to face the exam with confidence.
1. AZ-500 Microsoft Learning Platform
When you are looking for reliable resources, the first thing you have to do is visit the official Microsoft Site. This is where you will get all the information related to the exam. Also, you will get resources that are authentic and trustworthy. Most of your queries regarding any aspect of the exam can be solved by the information provided on this page. Therefore, you must regularly visit this page to stay updated about the exam.
2. Instructor-Led AZ-500 Training
Instructor-led training by Microsoft is a course where you get to train yourself under the guidance of an expert. This can be accessed remotely and you have the flexibility of studying at your pace. You can have these virtual classes arranged at your convenience. With the instructor-led course, it will be easier for you to pick up technical skills and conceptual knowledge. For further guidance, you can also check out our online tutorial for AZ-500.
3. AZ-500 Books
You can always go for the traditional way of studies. Books can be helpful for those who are more comfortable grasping the concepts via reading. You can try out the following books for the Microsoft Azure AZ-500 preparations –
- Pro Azure Governance and Security by Peter De Tender
- Microsoft Azure Security Infrastructure by Yuri Diogenes
4. AZ-500 Practice Tests
When you have done all your preparations, it is time to encapsulate all your knowledge and test it with practice tests. This is the last step of your preparations but is as important as any of the above-mentioned steps. Skipping this can lead to disastrous results. And mastering this step will make your success certain. Hence, it is advised to go for multiple practice tests to test your accuracy and speed. Test yourself now with a free practice test!