Are you planning to take a Certified Information Security Manager (CISM) examination? If so, it is time to get your teeth into one of the biggest opportunities in this sector. Information security has grown beyond a mere information exchange between organizations. It has evolved into an even greater need for protection against hackers, spammers, and other threats. In this blog, we will help you sail through all the required exam details require to prepare for the exam. Furthermore, we will be adding a few official learning resources to ease your process of preparation. So let us begin understanding the details of the exam.
CISM Exam Format
The Certified Information Security Manager (CISM) certification exam demonstrates in-depth knowledge and understanding of the relationship between information security programs and broader business goals and objectives. The CISM examination tests theoretical knowledge of the principles of an information security management system using a common set of core standards and criteria for measuring security practices.
Certified Information Security Manager Exam Details
Familairising with the exam dtails is essential to be thorough with the CISM exam pattern. The Certified Information Security Manager (CISM) exam consists of 150 multiple-choice questions. Candidates have to score at least 450 or more points to pass the exam. Moreover, the CISM exam duration is 4 hours. The CISM exam costs $575 USD for members and $760 for non-members which includes additional taxes. Also, the CISM exam questions are available in 4 languages, namely Chinese Simplified, English, Japanese, and Spanish.
- Name Certified Information Security Manager
- Exam Code CISM
- Duration 4 Hours
- Exam Format Multiple Choice and Multi-Response Questions
- Number of Questions 200 Questions
- Total Exam Fee $575 (members); $760 (non-members) + taxes
- Exam Language English, Spanish and Japanese
Certified Information Security Manager Course Outline
CISM certification guide covers the following topics that form the exam syllabus:
Information Security Governance
- Firstly, establish and maintain an information security strategy in alignment with organizational goals and objectives to guide the establishment and ongoing management of the information security program
- Secondly, establish and maintain an information security governance framework to guide activities that support the information security strategy
- Thirdly, integrate information security governance into corporate governance to ensure that organizational goals and objectives are supported by the information security program
- Then, establish and maintain information security policies to communicate management’s directives and guide the development of standards, procedures, and guidelines
- Further, develop business cases to support investments in information security
- Also, identify internal and external influences to the organization (for example, technology, business environment, risk tolerance, geographic location, legal and regulatory requirements) to ensure that these factors are addressed by the information security strategy
- Furthermore, obtain a commitment from senior management and support from other stakeholders to maximize the probability of successful implementation of the information security strategy
- Define and communicate the roles and responsibilities of information security throughout the organization to establish clear accountabilities and lines of authority
- Lastly, establish, monitor, evaluate and report metrics (key goal indicators [KGIs], key performance indicators [KPIs], key risk indicators [KRIs]) to provide management with accurate information regarding the effectiveness of the information security strategy
Managing Information Risk
- Firstly, establish and maintain a process for information asset classification to ensure that measures taken to protect assets are proportional to their business value
- Secondly, identify legal, regulatory, organizational, and other applicable requirements to manage the risk of noncompliance to acceptable levels
- Thirdly, ensure that risk assessment, vulnerability assessments, and threat analyses are conducted periodically
- Further, determine appropriate risk treatment options to manage risk to acceptable levels
- Then, evaluate information security controls to determine whether they are appropriate and effectively mitigate risk to an acceptable level
- Also, identify the gap between current and desired risk levels to manage risk to an acceptable level
- Integrate information risk management into business and IT processes (for example, development, procurement, project management, mergers, and acquisitions) to promote a consistent and comprehensive information risk management process across the organization
- Furthermore, monitor existing risk to ensure that changes are identified and managed appropriately
- Lastly, report noncompliance and other changes in information risk to appropriate management to assist in the risk management decision-making process
Information Security Program Development & Management
- Establish and maintain the information security program in alignment with the information security strategy
- Ensure alignment between the information security program and other business functions (for example, human resources [HR], accounting, procurement, and IT) to support integration with business processes
- Identify, acquire, manage and define requirements for internal and external resources to execute the information security program
- Establish and maintain information security architectures (people, process, technology) to execute the information security program
- Communicate and maintain organizational information security standards, procedures, guidelines, and other documentation to support and guide compliance with information security policies
- Establish and maintain a program for information security awareness and training to promote a secure environment and an effective security culture
- Integrate information security requirements into organizational processes (for example, change control, mergers and acquisitions, development, business continuity, disaster recovery) to maintain the organization’s security baseline
- Integrate information security requirements into contracts and activities of third parties to maintain the organization’s security baseline
- Establish, monitor, and periodically report program management and operational metrics to evaluate the effectiveness and efficiency of the information security program
Information Security Incident Management
- Establish and maintain an organizational definition of, and severity hierarchy for, information security incidents to allow accurate identification of and response to incidents
- Establish and maintain an incident response plan to ensure an effective and timely response to information security incidents
- Develop and implement processes to ensure the timely identification of information security incidents
- Establish and maintain processes to investigate and document information security incidents to be able to respond appropriately and determine their causes while adhering to legal, regulatory, and organizational requirements
- Establish and maintain incident escalation and notification processes to ensure that the appropriate stakeholders are involved in incident response management
- Organize, train, and equip teams to effectively respond to information security incidents promptly
- Test and review the incident response plan periodically to ensure an effective response to information security incidents and to improve response capabilities
- Establish and maintain communication plans and processes to manage communication with internal and external entities
- Conduct post-incident reviews to determine the root cause of information security incidents, develop corrective actions, reassess risk, evaluate response effectiveness and take appropriate remedial actions
- Establish and maintain integration among the incident response plan, disaster recovery plan, and business continuity plan
Now that you have all the details of exam all you need a good set of resources that will help you prepare and practice better to qualify the exam.
Certified Information Security Manager (CISM) Study Guide
The exam period is one of the times when you wish you had a 100% guarantee of passing. However, if you are going to put in the hard work, there is no harm in improving your chances. Here are a few ways to enhance your CISM exam preparation
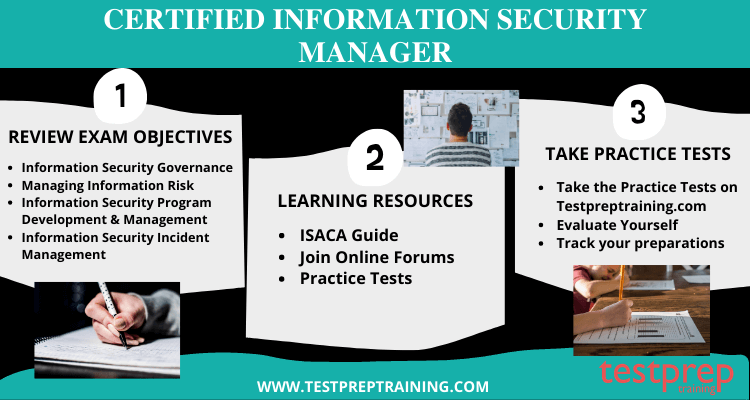
ISACA Guide
The ISACA Guide gives you a solid foundation for your learning experience. Then it is up to you to determine how much time and effort to invest based on your learning style. This guide is the most comprehensive source of material that you need to study. ISACA CISM exam guide provides you with an overview of what is covered in the exam. You get the information about resources for in-depth information on various topics. Further, you can get sample questions to help you refine your knowledge.
For better preparation you can also go for Certified Information Security Manager (CISM) Online Course
ISACA Journals
The ISACA journals are peer-reviewed publications based on research activities of members in the sector. They are available online, in print, or as an electronic collection. Some of the journals are available for free with registration and free membership. You can check our tutorial where we have described in detail the journals and other references for each topic in the syllabus.
Join the ISACA Community
To be a member of the ISACA online community is to connect with a global network that shares your passion. Members share knowledge, collaborate on research and news, and use their expertise to help fellow members solve pressing information technology assurance issues. Whether you are an expert or novice, a professional or student, there is an exclusive community designed to meet your needs.
Evaluate yourself with Practice Tests
Sitting for an exam you’re not familiar with can be nerve-racking. You want to do well, but you may feel unprepared or inadequate. This is a common feeling and one that often leads to anxiety. The best thing you can do at this time is to try and remain calm and focused. If you prepare yourself adequately, there is no need for you to feel anxious. By doing CISM exam sample questions regularly, you can reduce your anxiety about the exam. Also, you can measure your progress in terms of improvement over the weeks leading up to the actual test date. Test yourself with a free practice test now!